I recently faced a issue scenario where a Domain controller at a remote site became tombstoned after not having replicated with Active Directory for 60 days. Putting aside how I never noticed this, there was little I could do in this situation. It’s time had skewed out soo far that it stopped participating with replication. Whatever the issue, if a domain controller doesn’t communicate / replicate with AD within AD’s tombstone lifetime it will eventually become permanently tombstoned.
The default tombstone lifetime in Windows Server 2000 – 2003 is 60 days. In Windows Server 2003 SP1 and above it’s 180 days. Despite being Windows 2003 R2, the forest came from SBS 2003. The originally tombstone lifetime doesn’t change when you upgrade so it stayed 60 days.
The first part to fixing the issue was demoting the domain controller back to a standalone server. Once performed I could fix whatever issues the network had and re-promote at a later stage.
Even though the network was up and the domain controller in question could connect to other domain controllers. Being tombstoned meant that it wouldn’t talk with the DCs. Running the command dcpromo on the DC in question would fail when it attempted to communicate with the domain.
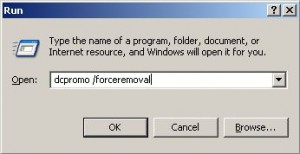
To work around the issue the command needed to be run with the /forceremoval switch.
Dcpromo /forceremoval
Below are the steps to perform a force removal.
1. Run dcpromo /forceremoval from the run box.
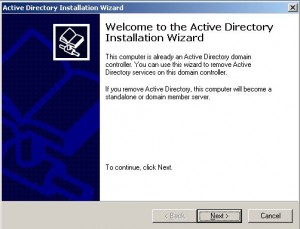
2. Click next to start the wizard.
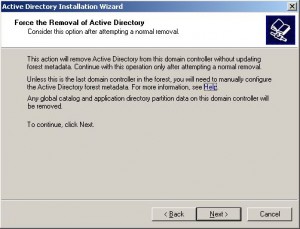
3. Confirm the removal.
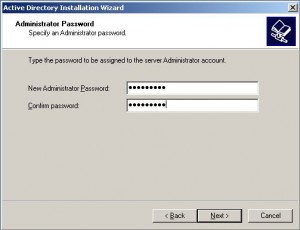
4. Sent a new administrator password for when the server becomes a standalone server.
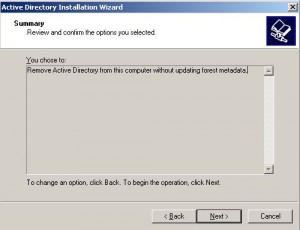
5. Confirm the removal of AD without cleaning up the metadata. This is an important step to note. Because we are forcing the removal of AD without cleanup up the metadata this is a manual step we will have to perform in our AD environment on a functioning DC.
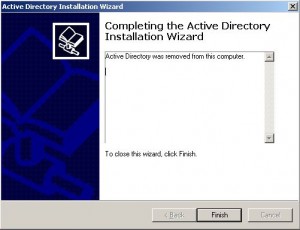
6. Demotion will now start and removal the server from being a Domain Controller.
7. Click finish and reboot the server to complete the process.
With the server now successfully demoted it can be promoted back to a domain controller using the standard dcpromo command. Before this can happen, though, we have to go back to step 5 above and perform a manual metadata cleanup of Active Directory to removal any references to this tombstoned DC. I’ll be covering this more indepth step in a later post. Microsoft has a very thorough article on how to perform this process
With the server demoted and a metadata cleanup performed I could happily promote this server back to a DC. Preventing the issue happening again would mean fixing my monitoring and sorting out any time sync issues… also a post for a later stage.
Appendix
Metadata cleanup
How to remove data in Active Directory after an unsuccessful domain controller demotion